Future Internet | Free Full-Text | RLXSS: Optimizing XSS Detection Model to Defend Against Adversarial Attacks Based on Reinforcement Learning | HTML
Future Internet | Free Full-Text | RLXSS: Optimizing XSS Detection Model to Defend Against Adversarial Attacks Based on Reinforcement Learning | HTML

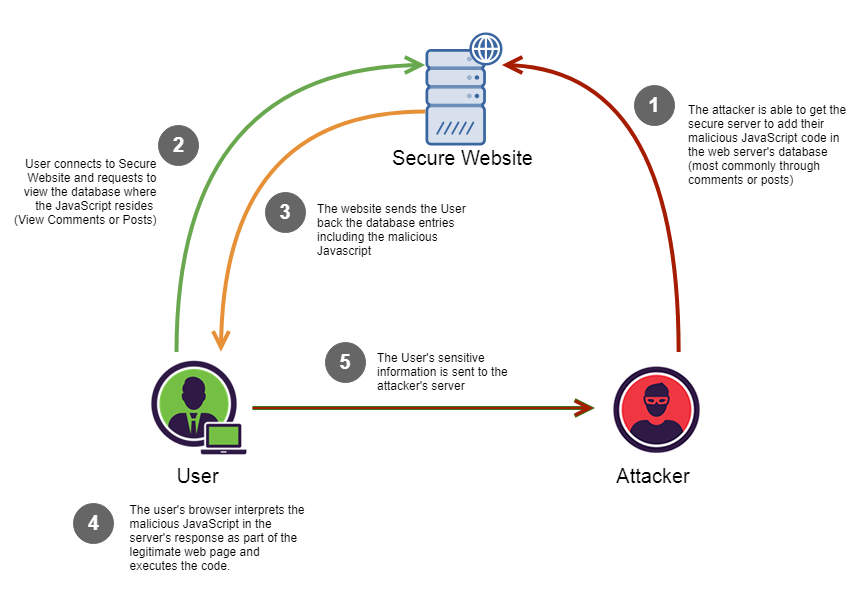
XSS‐immune: a Google chrome extension‐based XSS defensive framework for contemporary platforms of web applications - Gupta - 2016 - Security and Communication Networks - Wiley Online Library
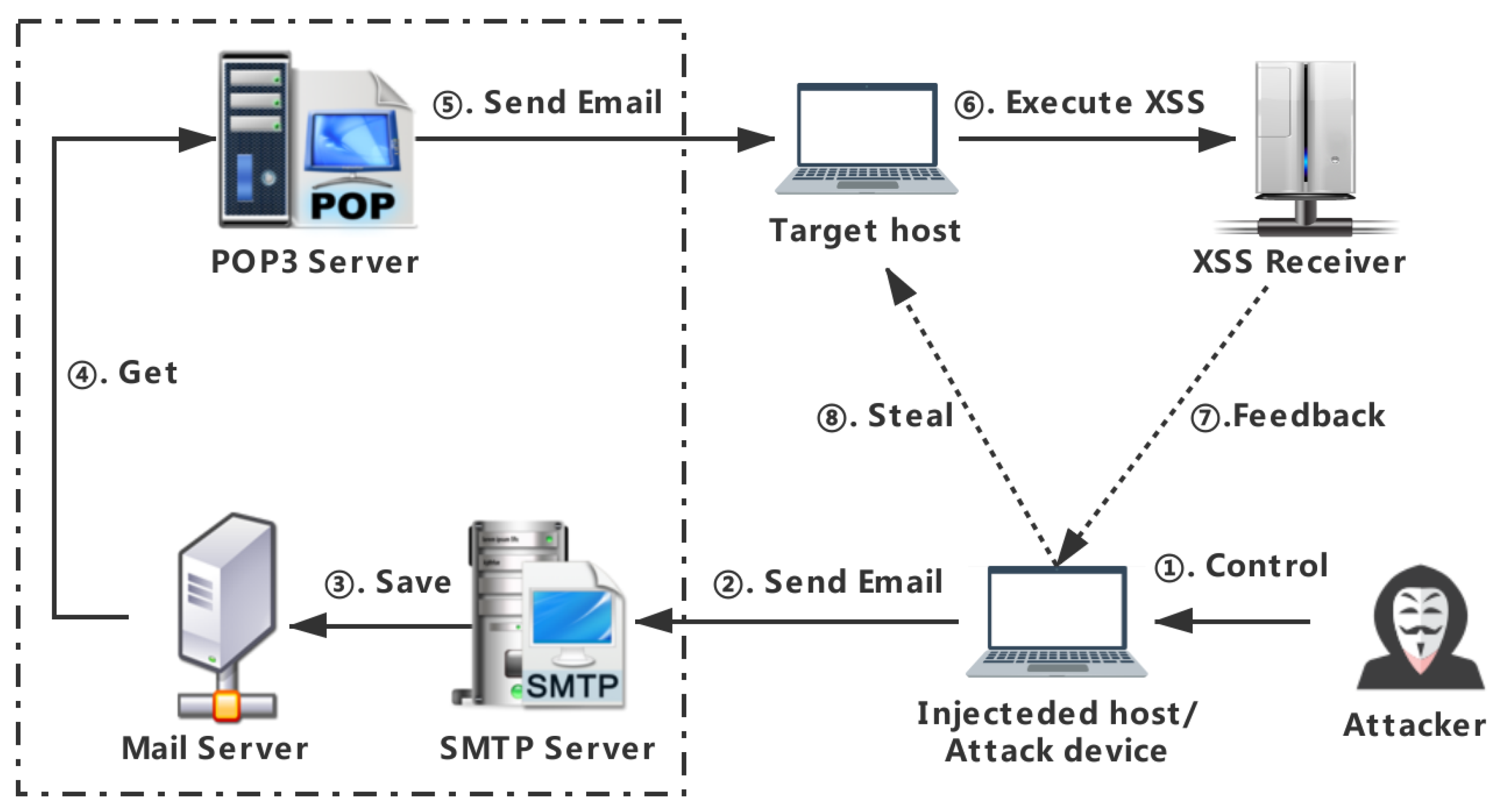
Applied Sciences | Free Full-Text | Providing Email Privacy by Preventing Webmail from Loading Malicious XSS Payloads | HTML
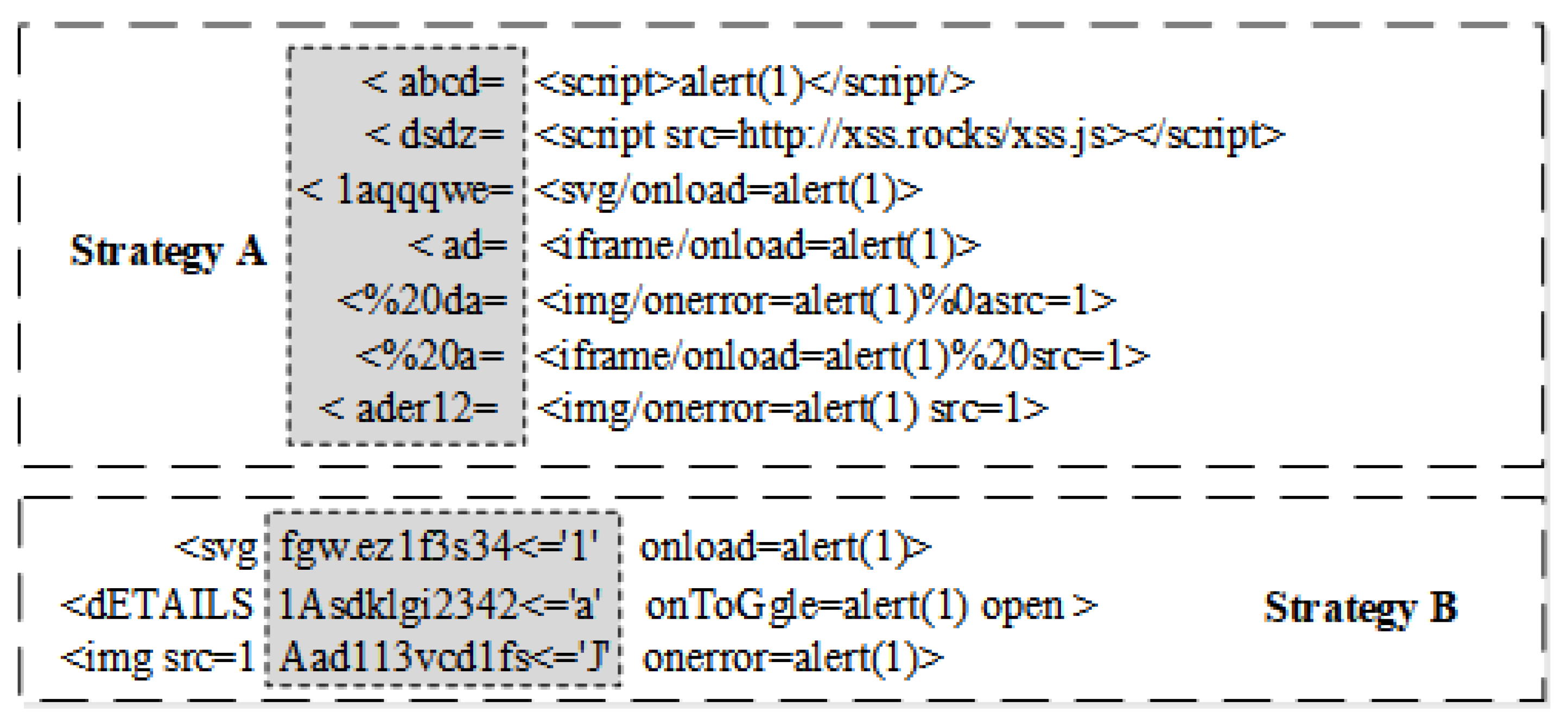





![PDF] Structural Learning of Attack Vectors for Generating Mutated XSS Attacks | Semantic Scholar PDF] Structural Learning of Attack Vectors for Generating Mutated XSS Attacks | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/2e55d5da4a4911e3c88781eae2e28604fc32d397/4-Figure2-1.png)