3.0.1 forces entry of device Gen Application Key? - ChirpStack Network Server - ChirpStack Community Forum

LoRa/Radio Remote Control Android Code Generator using <a href="https://play.google.com/store/apps/details?id=au.com.forward.pfodDesignerV2" target="blank">pfodDesignerV3</a> / <a href="https://play.google.com/store/apps/details?id=au.com.forward ...
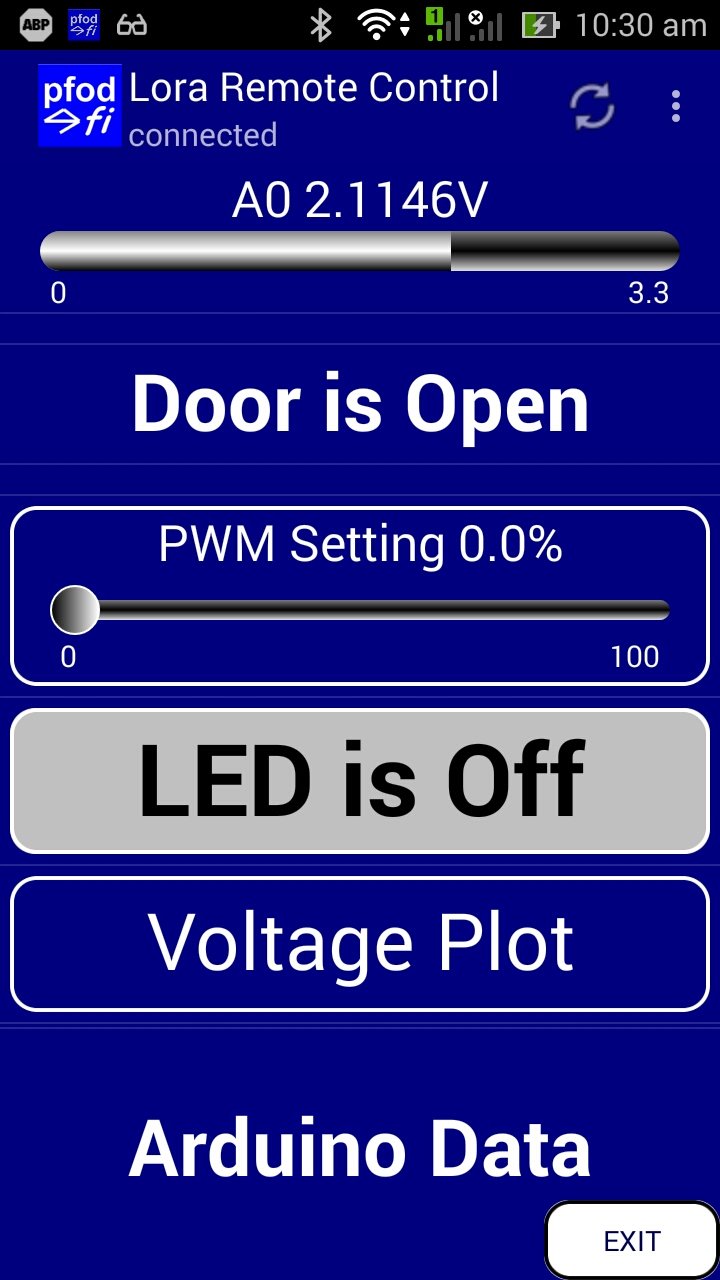
LoRa/Radio Remote Control Android Code Generator using <a href="https://play.google.com/store/apps/details?id=au.com.forward.pfodDesignerV2" target="blank">pfodDesignerV3</a> / <a href="https://play.google.com/store/apps/details?id=au.com.forward ...
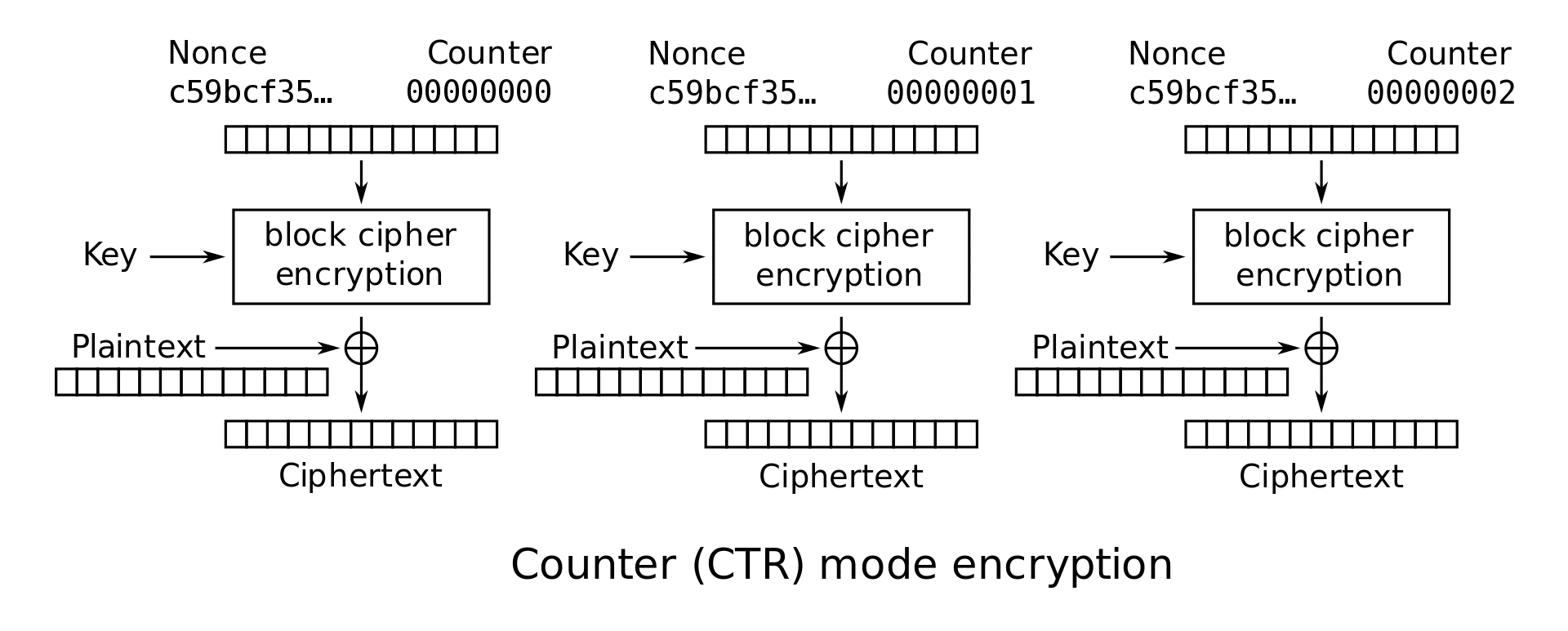
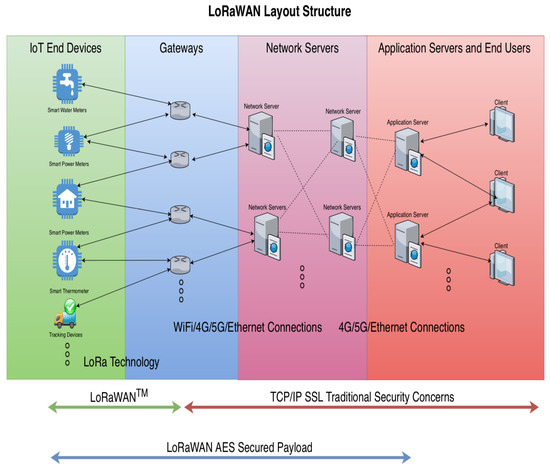
A Novel Secure Root Key Updating Scheme for LoRaWANs Based on <italic>CTR_AES</italic> DRBG 128

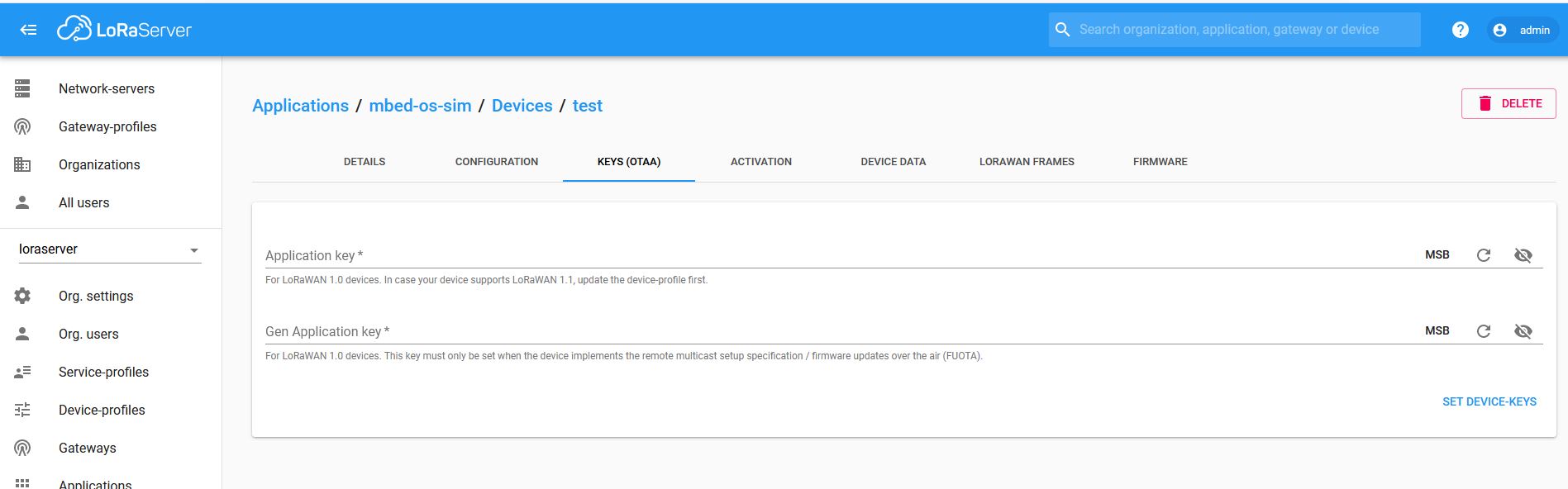
3.0.1 forces entry of device Gen Application Key? - ChirpStack Network Server - ChirpStack Community Forum
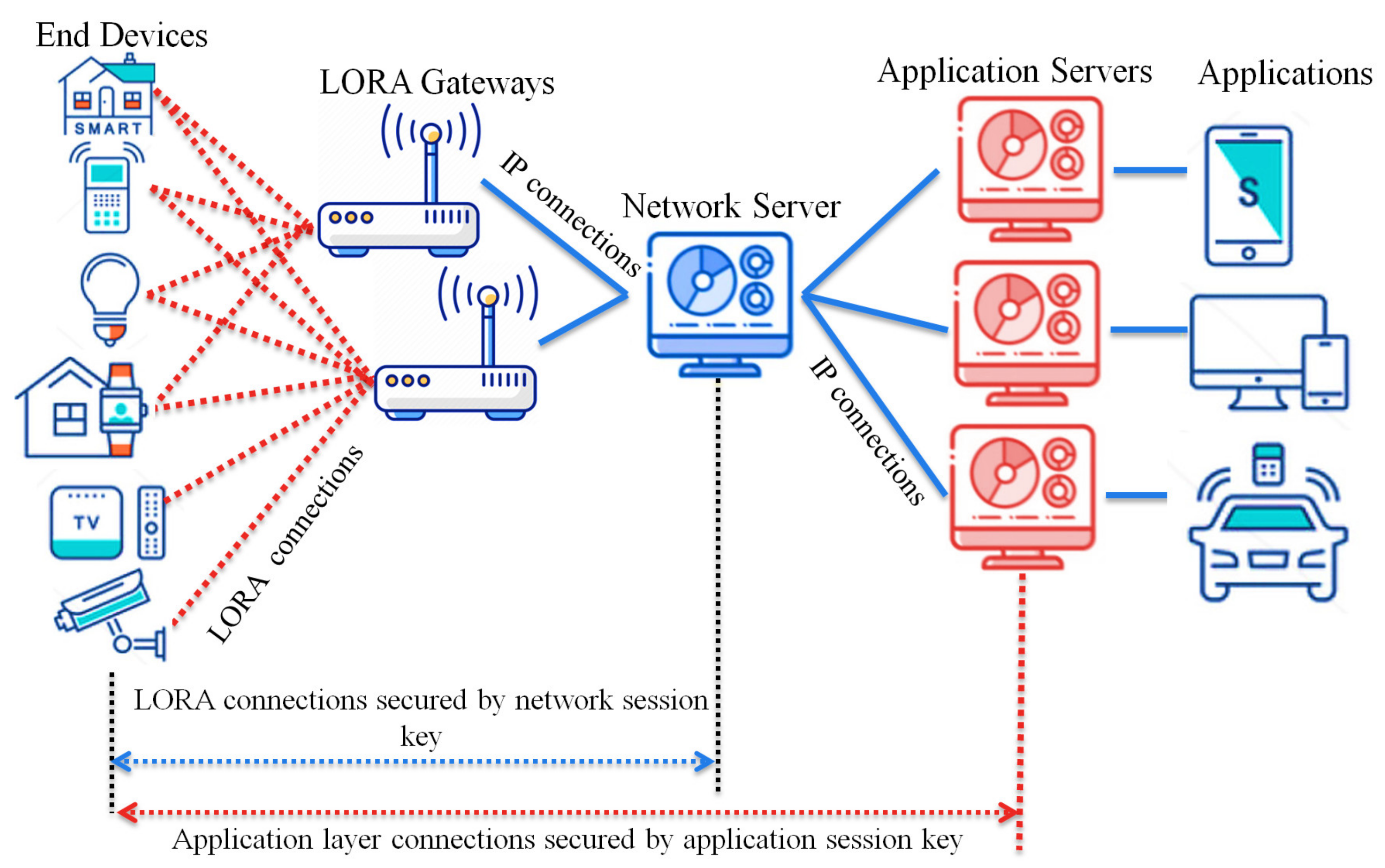

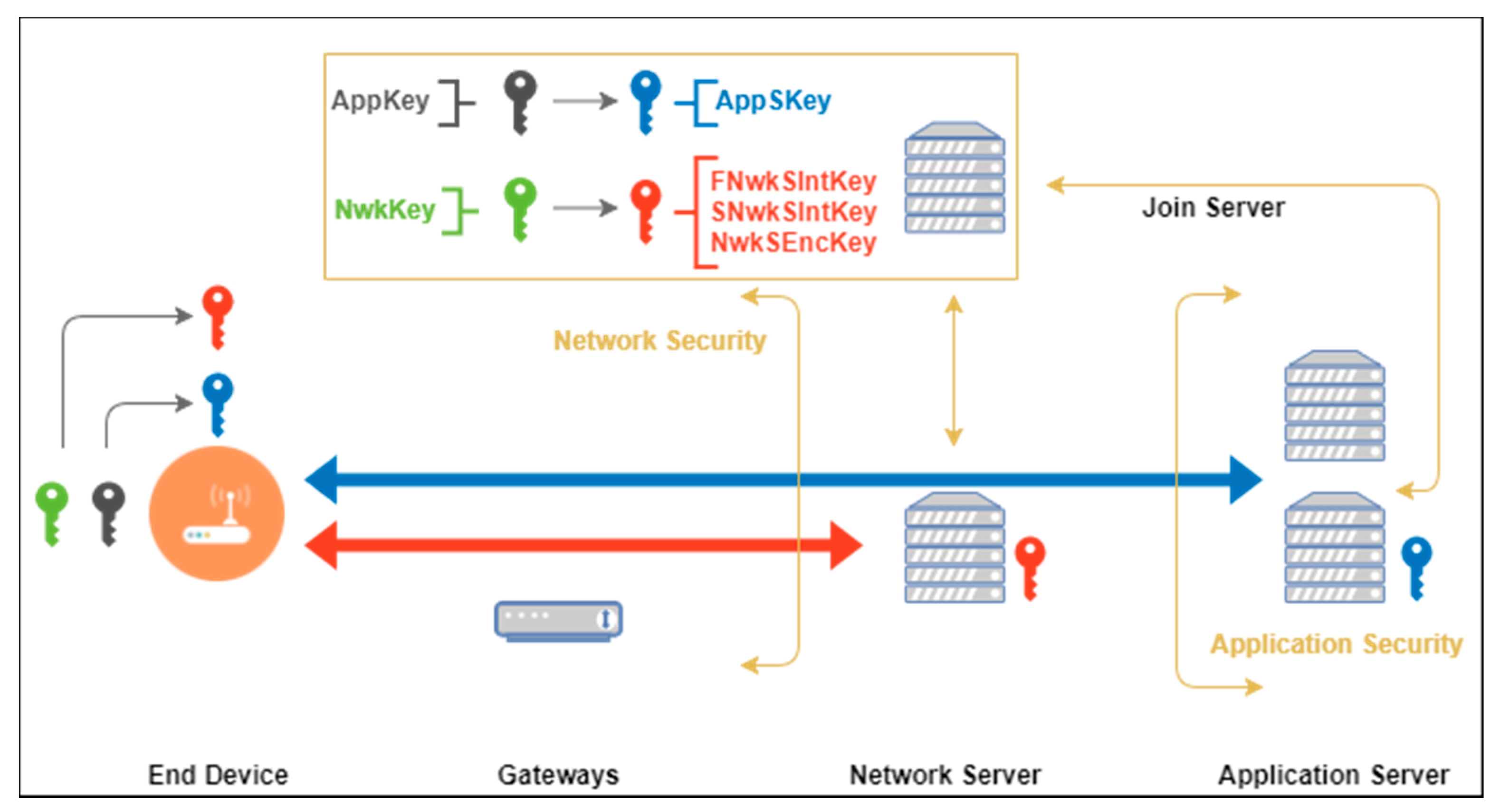
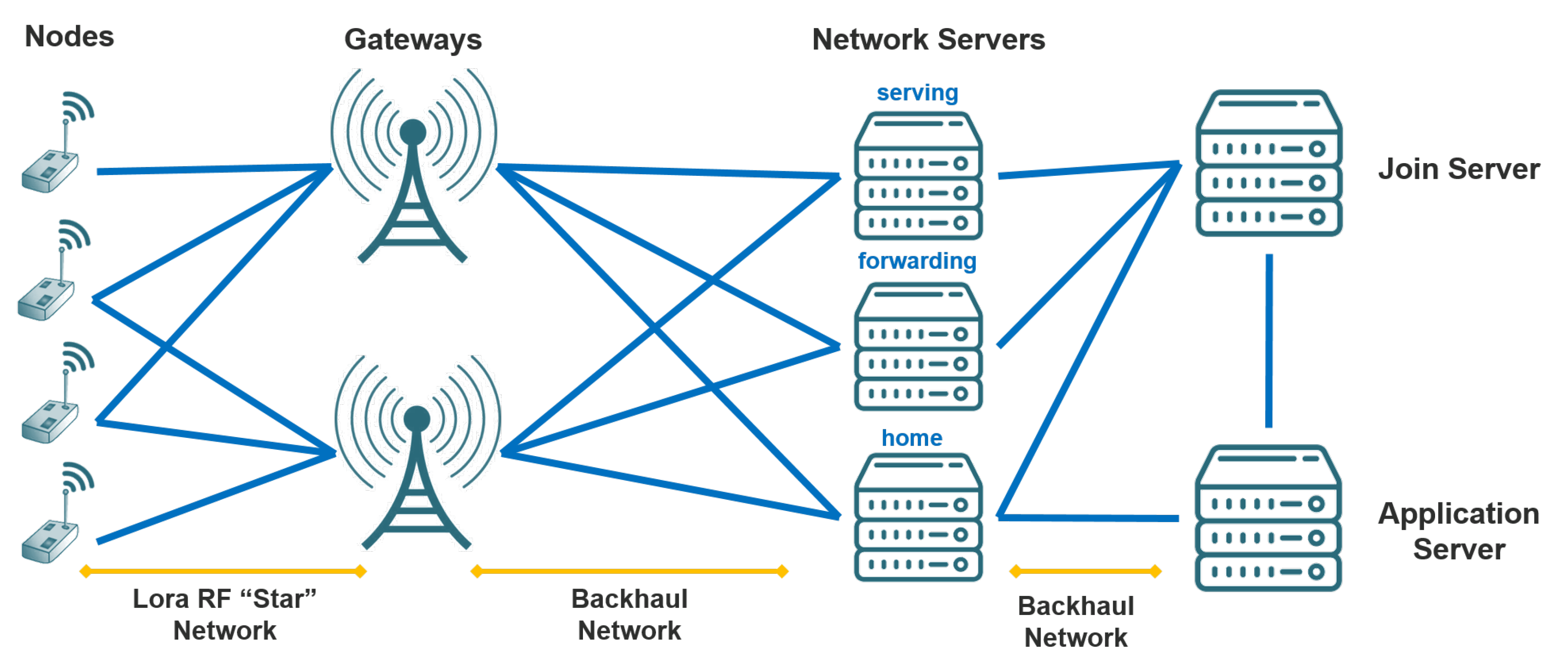
![AppSKey and NwkSKey are used for data integrity and security [23]. | Download Scientific Diagram AppSKey and NwkSKey are used for data integrity and security [23]. | Download Scientific Diagram](https://www.researchgate.net/publication/335873118/figure/fig1/AS:804283800899585@1568767609456/AppSKey-and-NwkSKey-are-used-for-data-integrity-and-security-23.png)






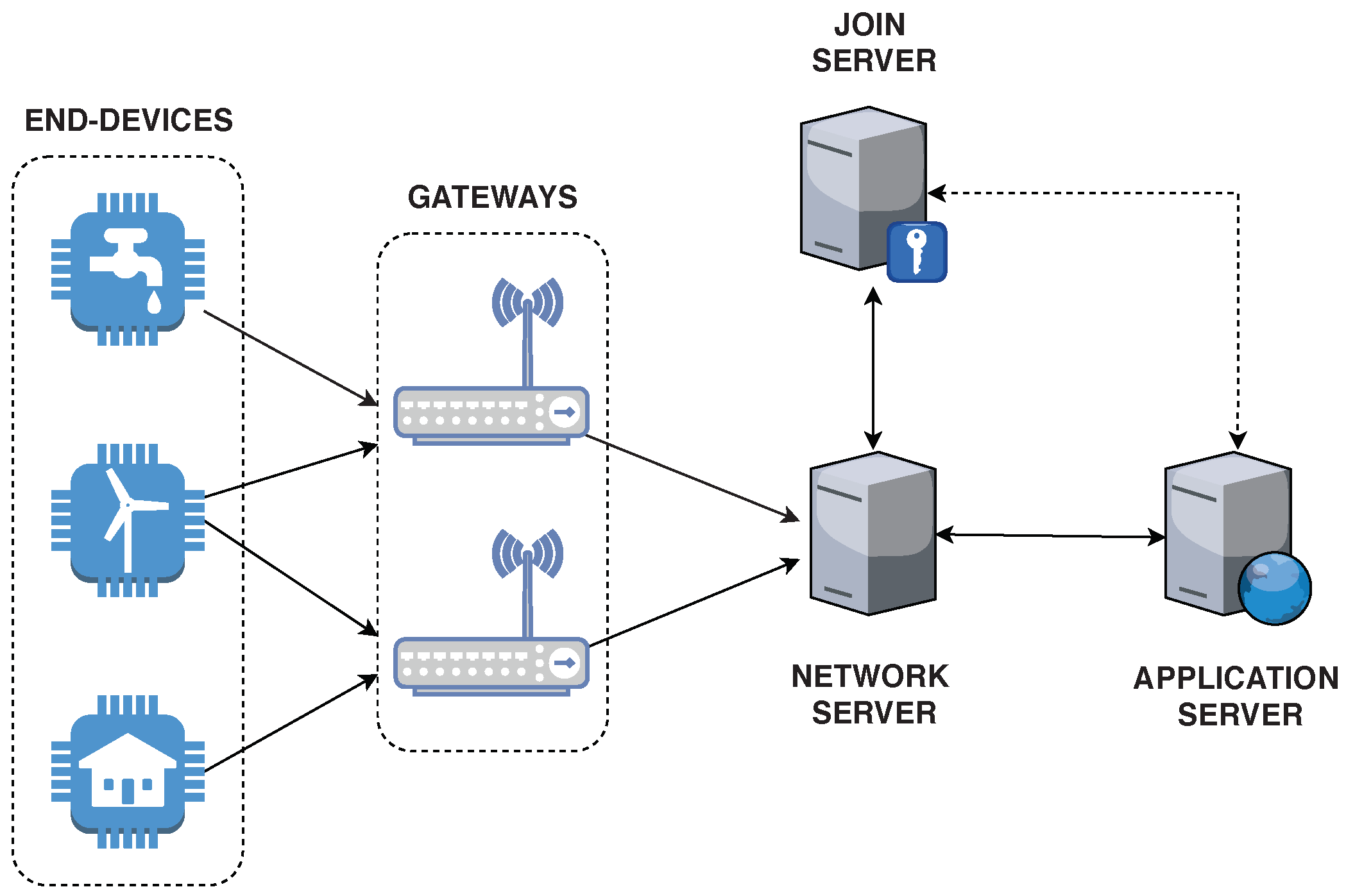
![PDF] A Dual Key-Based Activation Scheme for Secure LoRaWAN | Semantic Scholar PDF] A Dual Key-Based Activation Scheme for Secure LoRaWAN | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/2517dca0527281f279806d05fbb4d05e92673849/3-Figure1-1.png)