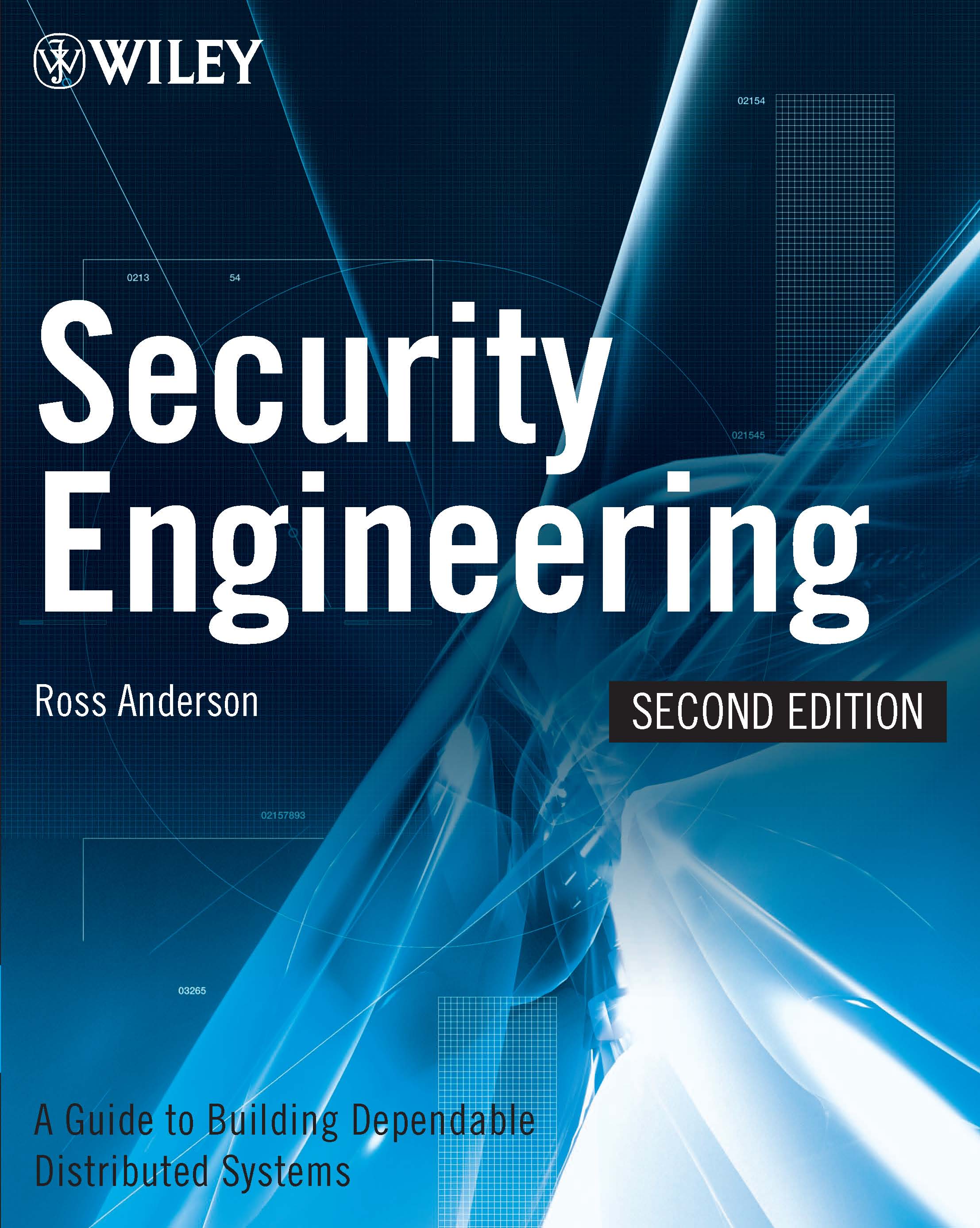
Introduction to Computer Security CSCE 4550/5550 Fall 2013 The aim of this course is to introduce the concepts and principles of

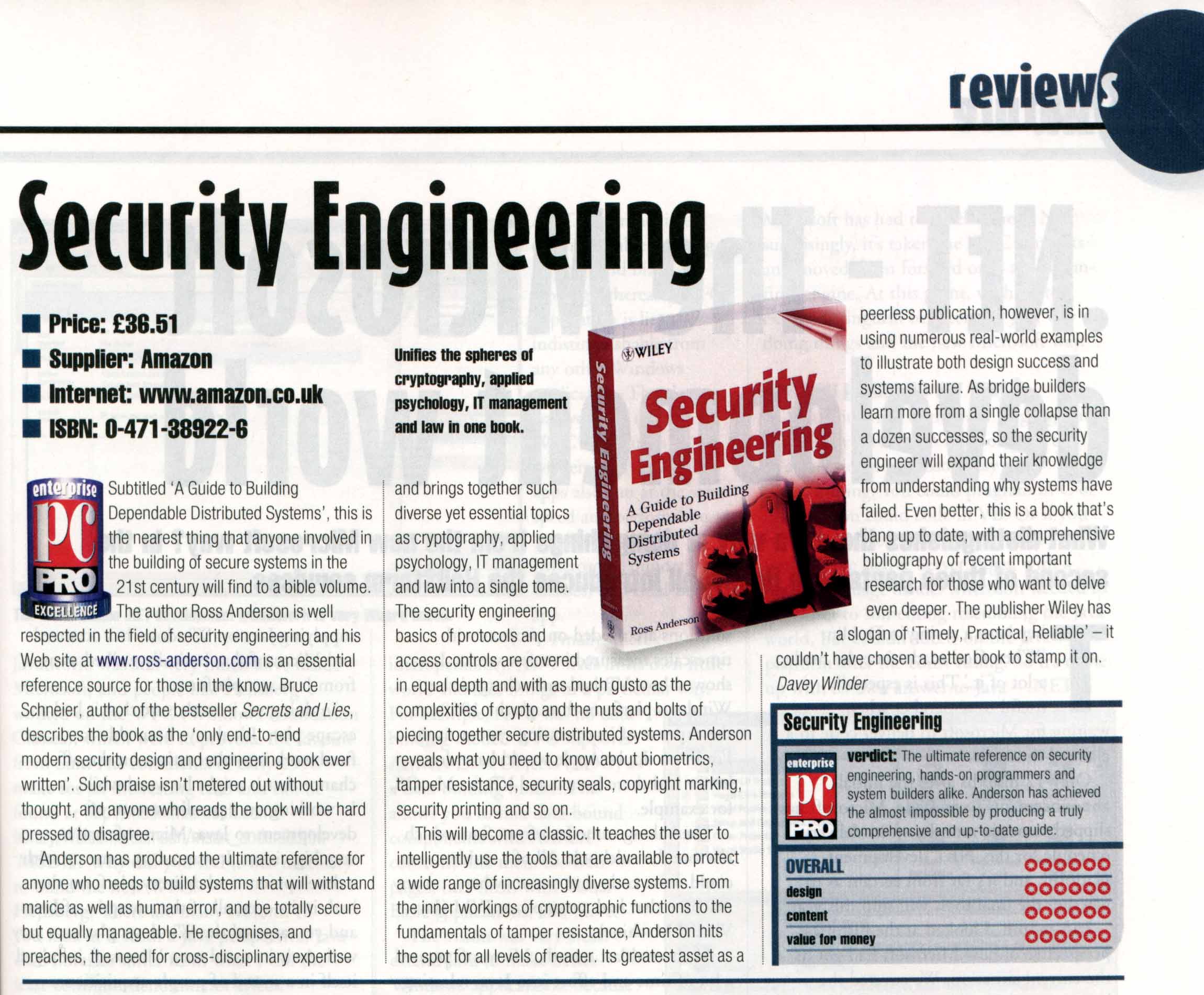
Security Engineering: A Guide to Building Dependable Distributed Systems: Anderson, Ross: 9781119642787: Amazon.com: Books
Wetootwaag's Bagpipe and History Podcast: Season 5 Episode 10 Jackson playthrough part 2 & Drops of Brandy Deep Dive
GitHub - vicoyeh/pointers-for-software-engineers: A curated list of topics to start learning software engineering
San José State University School/Computer Science CS 166, Information Security, Section 01, Fall, 2016
Wetootwaag's Bagpipe and History Podcast: s5e28 The Gravel Walk To Kiss Mother with Tunes from Frankie Kennedy & Mairéad Ní Mhaonaigh and Tim Britton

Building a Modern TRNG | Proceedings of the 4th ACM Workshop on Attacks and Solutions in Hardware Security
What Every Programmer Needs To Know About Security and Where To Learn It” Neil Daswani October ppt download