How to Hack Wi-Fi: Get Anyone's Wi-Fi Password Without Cracking Using Wifiphisher « Null Byte :: WonderHowTo

Con Watch: Why a Hacked Router Is “The Worst Thing That Can Happen to Computer Users” | The Saturday Evening Post

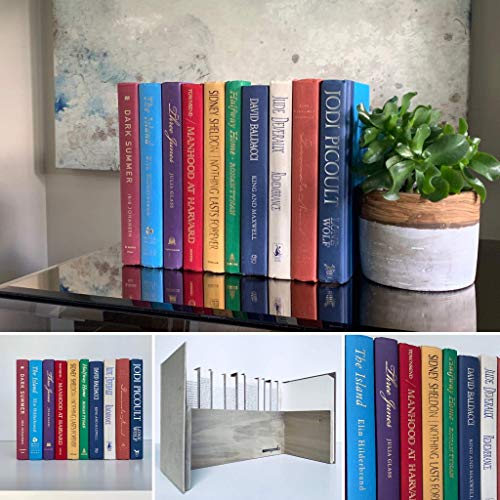
Amazon.com: ASUS ROG Rapture WiFi Gaming Router (GT-AC5300) - Tri Band Gigabit Wireless Router, Quad-Core CPU, WTFast Game Accelerator, 8 GB Ports, AiMesh Compatible, Included Lifetime Internet Security : Electronics