CYBER ATTACK DETECTION AND CLASSIFICATION USING MACHINE LEARNING TECHNIQUE USING MICROSOFT AZURE CLOUD

CTF Generator: Low private exponent (d) in RSA … the Wiener attack | by Prof Bill Buchanan OBE | ASecuritySite: When Bob Met Alice | Medium





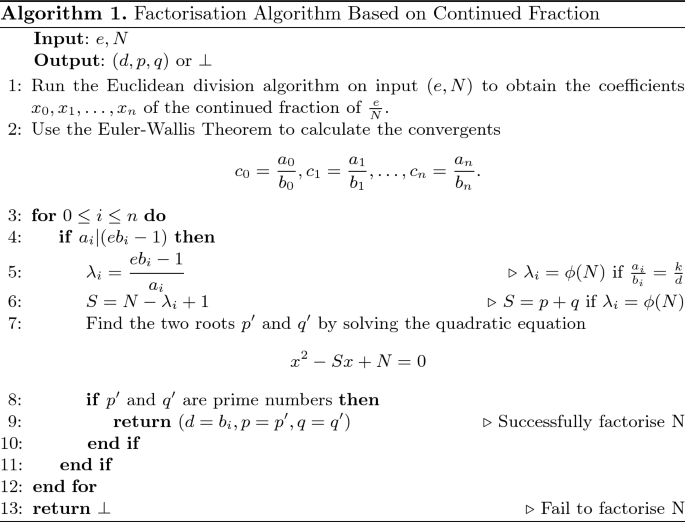
![PDF] On the Improvement of Wiener Attack on RSA with Small Private Exponent | Semantic Scholar PDF] On the Improvement of Wiener Attack on RSA with Small Private Exponent | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/2c5c7ae179350b71361bf93f9a00d4f8f073f6a6/7-Figure1-1.png)



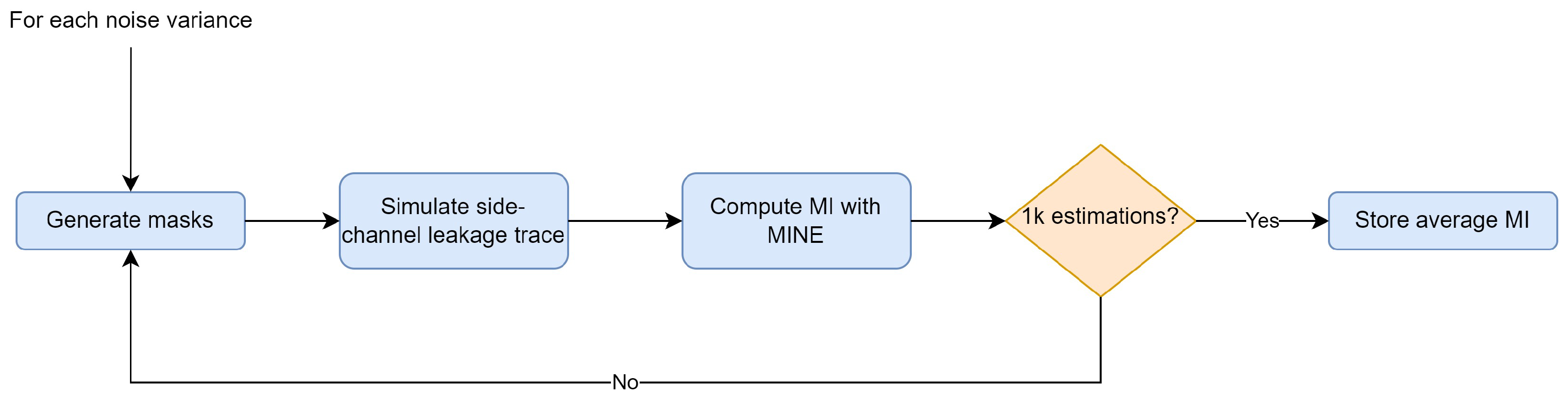
![PDF] On the Improvement of Wiener Attack on RSA with Small Private Exponent | Semantic Scholar PDF] On the Improvement of Wiener Attack on RSA with Small Private Exponent | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/2c5c7ae179350b71361bf93f9a00d4f8f073f6a6/6-Table2-1.png)

![PDF] On the Improvement of Wiener Attack on RSA with Small Private Exponent | Semantic Scholar PDF] On the Improvement of Wiener Attack on RSA with Small Private Exponent | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/2c5c7ae179350b71361bf93f9a00d4f8f073f6a6/6-Table1-1.png)

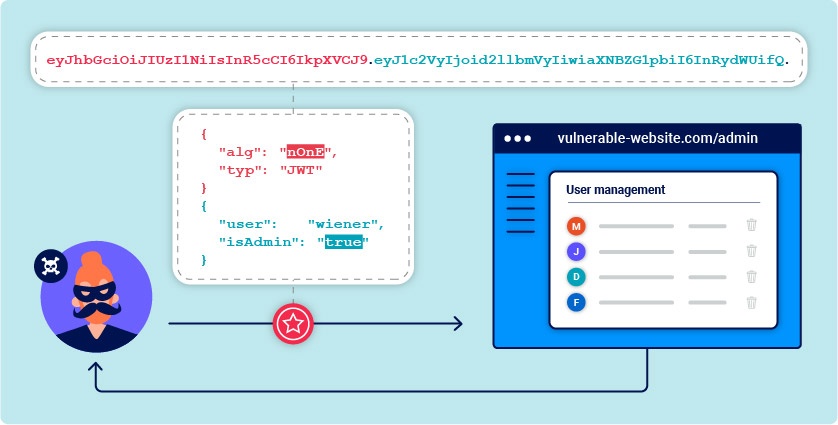
![PDF] On the Improvement of Wiener Attack on RSA with Small Private Exponent | Semantic Scholar PDF] On the Improvement of Wiener Attack on RSA with Small Private Exponent | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/2c5c7ae179350b71361bf93f9a00d4f8f073f6a6/7-Table3-1.png)