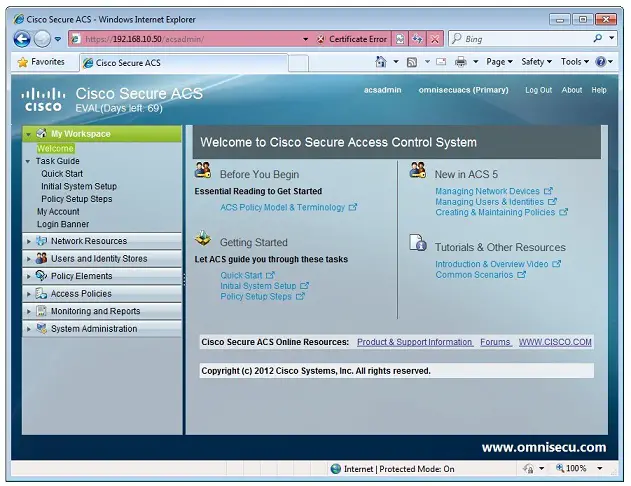
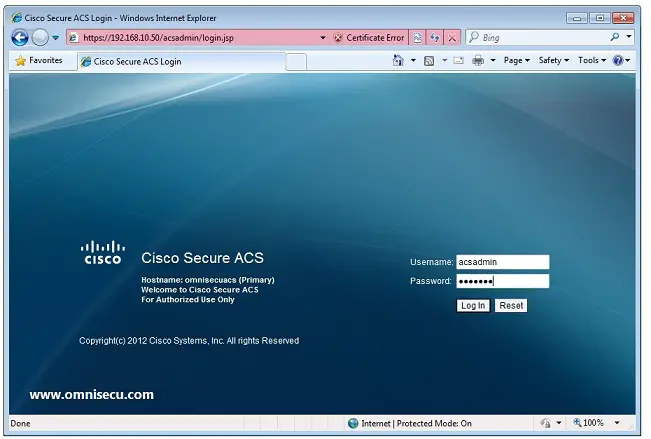
The Cisco Secure ACS and its configuration. The AP was configured to... | Download Scientific Diagram

ACS 5.x: TACACS+ Authentication and Command Authorization based on AD group membership Configuration Example - Cisco
![User Guide for Cisco Secure ACS for Windows 4.0 - Overview [Cisco Secure Access Control Server for Windows] - Cisco Systems User Guide for Cisco Secure ACS for Windows 4.0 - Overview [Cisco Secure Access Control Server for Windows] - Cisco Systems](https://www.cisco.com/en/US/i/100001-200000/130001-140000/138001-139000/138890.jpg)
User Guide for Cisco Secure ACS for Windows 4.0 - Overview [Cisco Secure Access Control Server for Windows] - Cisco Systems
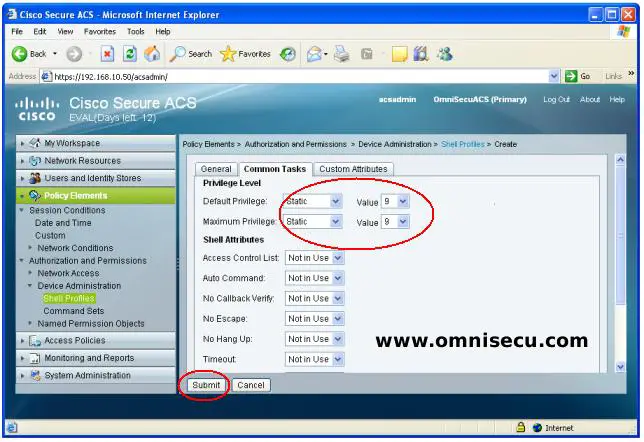
Cisco Secure ACS Shell Profiles and Command sets, How to configure Shell Profiles and Command sets in ACS

Example for Configuring Authentication for Telnet Login Users (Using the Secure ACS as a RADIUS Authentication Server) - S600-E Series Switches Typical Configuration Examples - Huawei