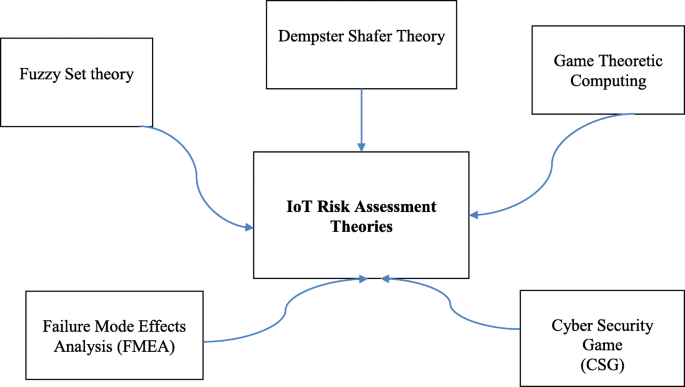
IoT cyber risk: a holistic analysis of cyber risk assessment frameworks, risk vectors, and risk ranking process | EURASIP Journal on Information Security | Full Text
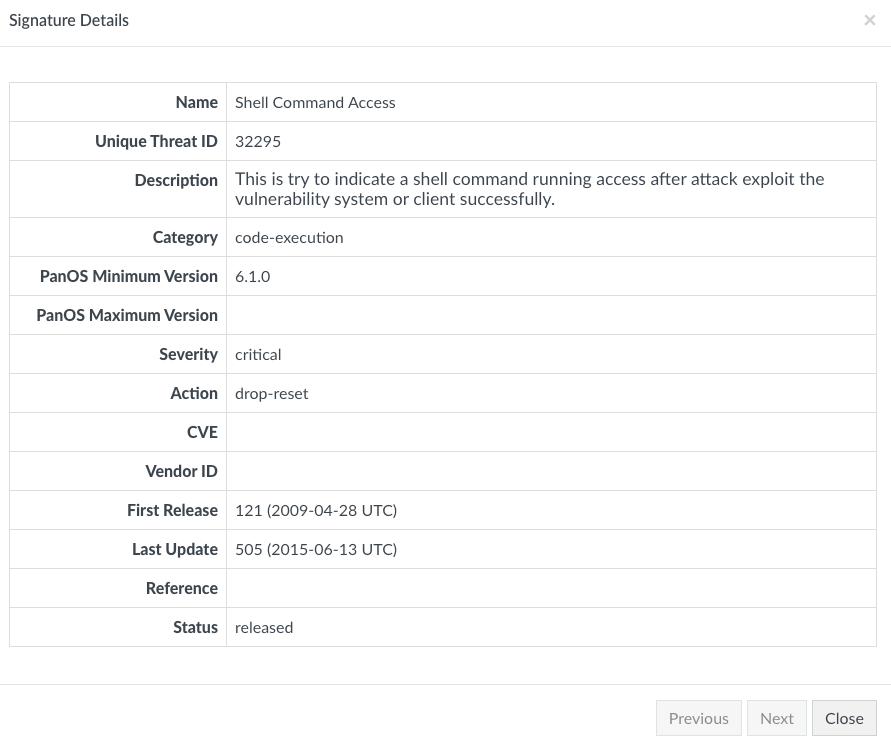
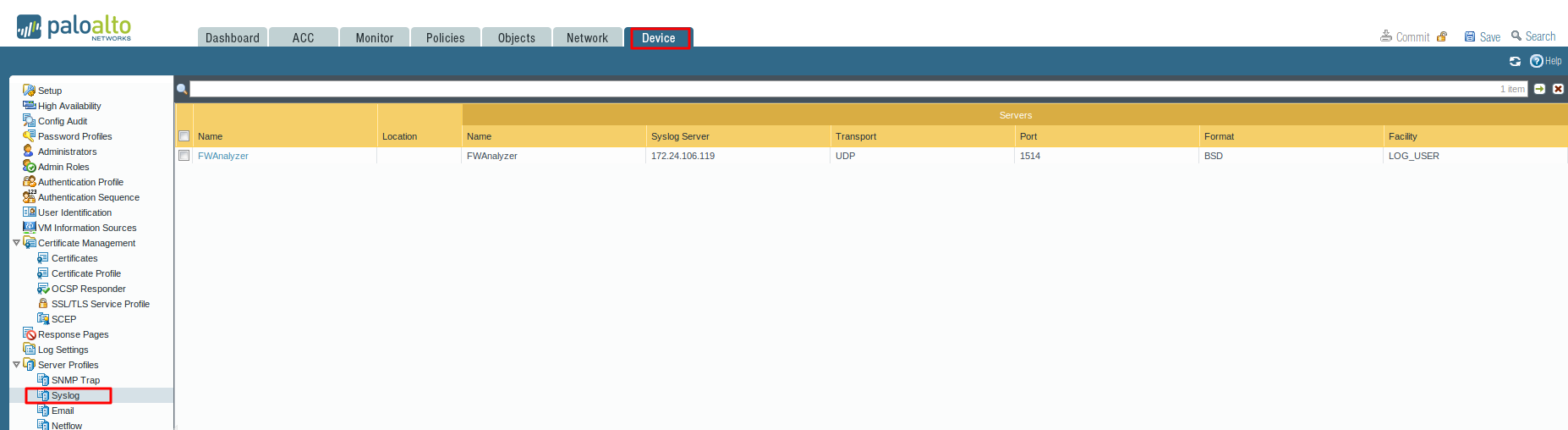
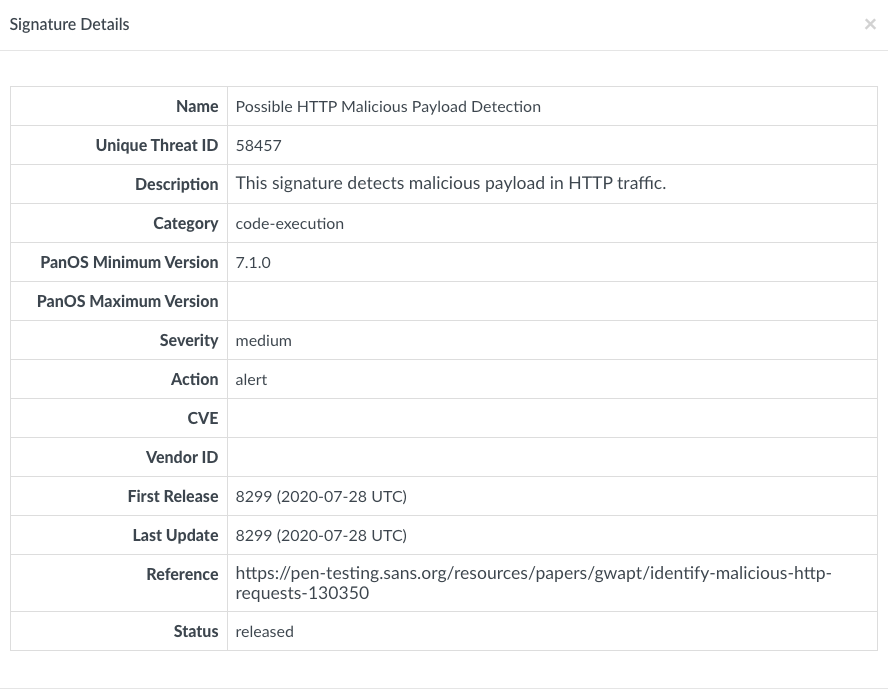
Mitigate Vulnerabilities Through Proper Application of Threat P... - Knowledge Base - Palo Alto Networks

ATC/DME test set for engineering, validation, test applications introduced by Cobham AvComm | Military Aerospace
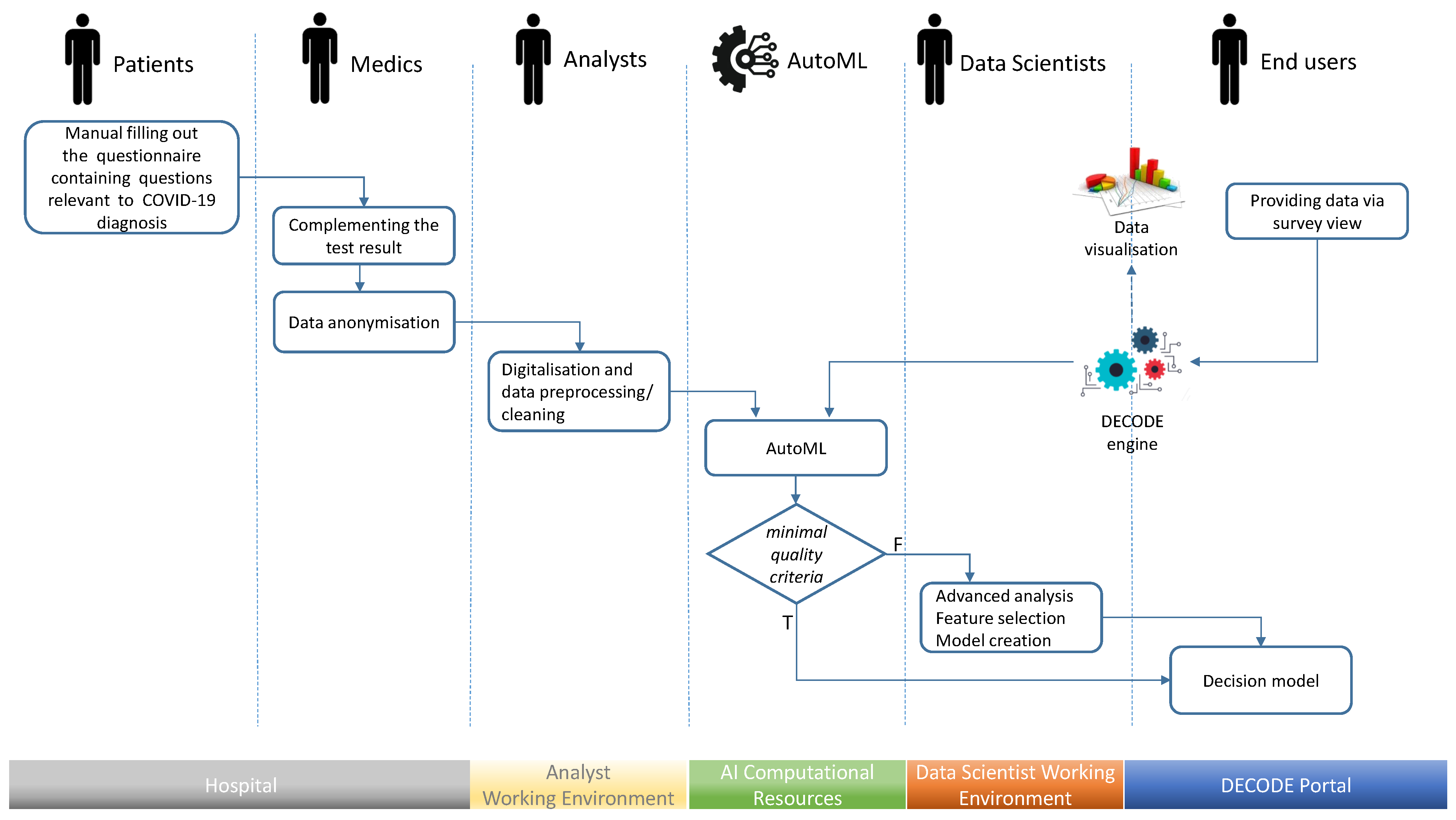
Applied Sciences | Free Full-Text | Screening Support System Based on Patient Survey Data—Case Study on Classification of Initial, Locally Collected COVID-19 Data | HTML

Systematic threat assessment and security testing of automotive over-the-air (OTA) updates - ScienceDirect